Use Active Directory to Control Access to Google Cloud VMware Engine Private Clouds
You can improve the security posture of your Google Cloud VMware Engine private cloud by setting up Active Directory authentication to allow for better visibility into actions by individual vSphere admins.
Default Admin Credentials
Google Cloud VMware Engine private clouds include one vCenter admin account called CloudOwner@gve.local that can be used for initial configuration tasks. That account does not have full administrative permissions, so in order to make certain impactful changes to the configuration, it is necessary to temporarily elevate the privileges using the feature in the GCVE portal as shown below.

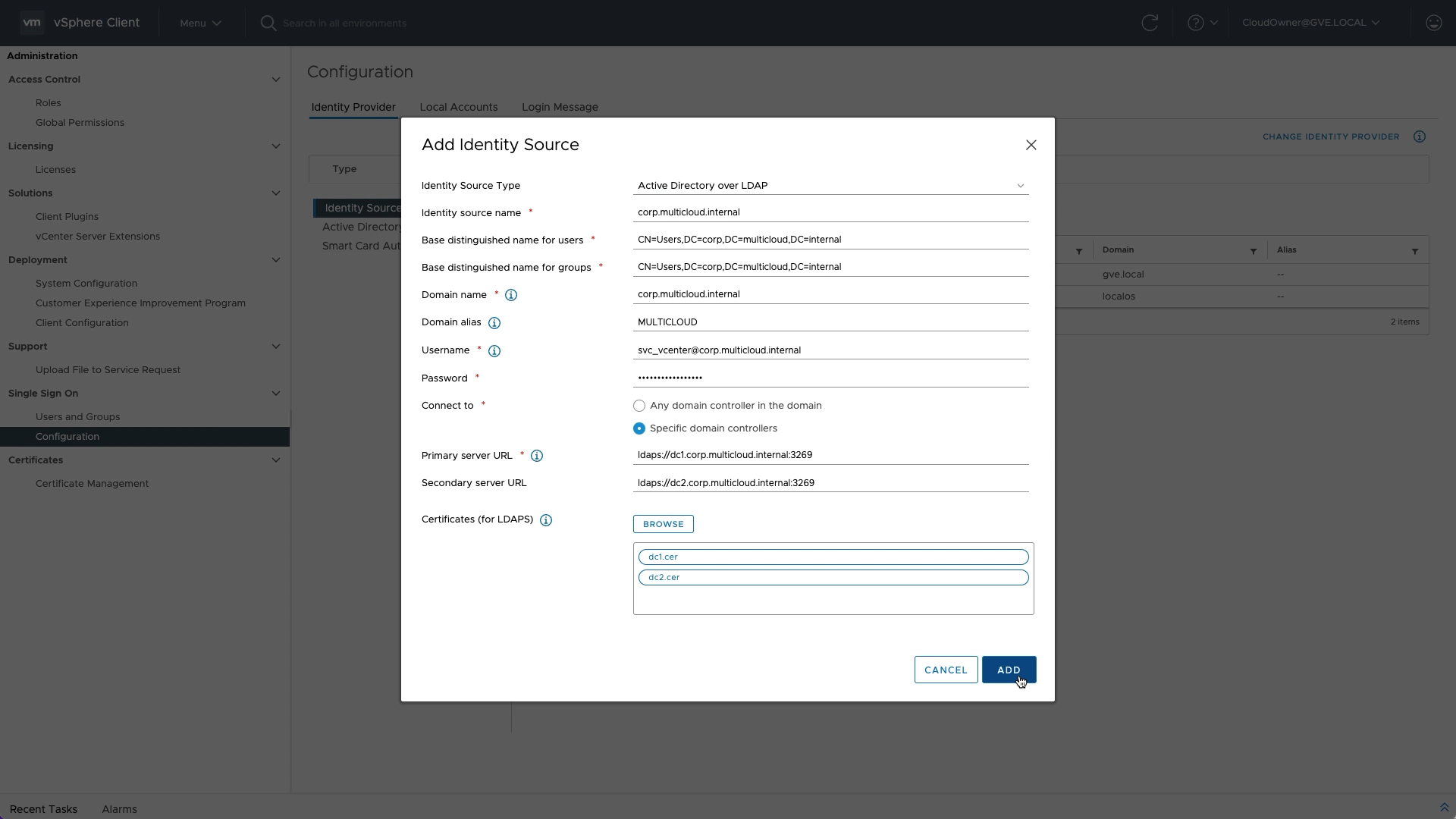
Changing identity sources is one task that requires additional rights. Once the elevated privileges have been granted, administrators can log in and configure Active Directory as an identity source. Because Google Cloud VMware Engine is based on the familiar VMware vSphere infrastructure stack, your existing knowledge and skills that you have built up from experience in your own data centers are still applicable in the cloud! Check out VMware KB article 2041378 for additional details on this configuration.

Keep in mind that bi-directional DNS forwarding should be configured before attempting to set up AD authentication so that names are used and not IP addresses.
Technical Demo
To see the entire workflow, as well as a couple of different options for configuring users, groups, and permissions, check out this short technical demo:
Takeaway
As an IT professional, you are entrusted with the security of your enterprise. For best accountability, do not allow multiple administrators to log in with a shared admin account - grant access to individuals so access can be audited, and ultimately revoked, when necessary.
