Security Introduction
Introduction
Information security is, at its core, defined by three main concepts: confidentiality, integrity, and availability. Organizations often think about “security” primarily in terms of confidentiality, but omitting the other concepts leaves out many essential design ideas that help supply resilience to systems, during incidents ranging from a security breach to a natural disaster. The concepts also interrelate. For example, designing for availability often means that resolving vulnerabilities is easier, helping to restore confidentiality and integrity to systems. Thinking about security in the cloud means thinking about, and designing for, all three data security concepts.
Security is a process that belongs to everyone in IT and technology, not just the “security team” or the chief information security officer (CISO). This is especially true in small and medium-sized businesses that may not have a separate security team. Regardless of an organization’s size, cloud and virtual infrastructure administrators are often the primary implementers of security controls in an organization, while the security team sets policy, audits for compliance, and conducts incident response. Everyone within the organization participates in the process in some way. As such, the information presented here is intended to aid everyone in gaining an understanding of security design principles, and how they apply to operations in the VMware Cloud.
Information Security Concepts
An understanding of information security concepts enables efficient communication within organizations, promotes understanding among different groups within an organization, and improves system design by highlighting areas of consideration.
Authentication
The ability to prove that a person or application is genuine, verifying the identity of that person or application. Authentication uses one or more of three primary methods, or factors: what you know, what you are, and what you have.
“What you know” encompasses passwords, personal identification numbers (PINs), passphrases, and other secrets. This type of authentication is not strong on its own and is typically paired with another authentication factor.
“What you are” involves biometric authentication methods, such as retinal scans, fingerprints, voice or signature recognition, and so on. These factors cannot be easily changed if compromised.
“What you have” entails objects or applications running on objects that you physically possess. Traditionally this involved keys, but modern forms may also involve USB tokens, smart cards, and one-time password applications on devices. This factor requires possession of the object at the time of use and may be hindered by intentional or unintentional loss of, or damage to, the object.
Multi-Factor Authentication is a method that uses authentication techniques from more than one factor. For example, combining a password with a one-time password application, or a facial scan with a PIN. This approach helps mitigate weaknesses in the use of each factor. Use of two techniques from the same factor, such as two passwords or two physical keys, is not considered multi-factor.
Authorization
The act of determining whether a user or application has the right to conduct particular activities in a system, relying on authentication to prove the identification of the user or application.
Availability
Ensuring that data is available to authorized parties when needed.
Compensating Control
Security and privacy controls implemented as an alternate solution to a requirement that is not workable for an organization to implement in its original form. The sum of the compensating controls must meet the intent and requirements of the original security control.
Confidentiality
Ensuring that data is protected from access by unauthorized parties.
Data Breach
An incident where data is accessed, copied, transmitted, viewed, or stolen by an unauthorized party. This term does not indicate intent; other terms such as “data leak” and “information leakage” help convey whether a data breach was intentional or not.
Identification
The ability to uniquely prove who a user of a system or application is, to enforce access control and establish accountability.
Incident
The attempted or successful unauthorized access, use, disclosure, modification, or destruction of information or interference with system operations. Note that this is not limited to people, nor does it indicate intent; natural phenomena, disasters, and animals can also cause incidents, for example.
Integrity
Ensuring that data is protected against unauthorized modification.
Lateral Movement
A method of describing the techniques used by attackers, after breaching an endpoint or system, to “pivot” and extend access to other systems and applications in their target organization. This moves the attacker closer to their goals, such as accessing, changing, exfiltrating, or destroying sensitive information.
Least Privilege
Only assigning the minimum access rights that are necessary for staff or systems to perform their authorized tasks, for the minimum duration necessary.
Non-repudiation
The ability to associate messages, actions, and/or authentications with an individual in a way that cannot be denied by that individual.
Recovery Point Objective (RPO)
The largest amount of data that is acceptable to lose after recovering from an incident. This is measured in time, e.g. “one hour of customer data.”
Recovery Time Objective (RTO)
The largest amount of time that is acceptable for data to be unavailable due to an incident.
Security Control
A safeguard or countermeasure designed to protect the confidentiality, integrity, and availability of data.
Separation of Duties
Dividing critical functions among different staff to help ensure that no individual has enough information or access to conduct fraud.
Vulnerability
A weakness in an information security system, system security procedures, security controls, or implementations that could be exploited by a threat actor.
Shared Responsibility Model
Whenever there are multiple groups working together on a system it is helpful to define roles and responsibilities. The Shared Responsibility Model does that for VMware Cloud, helping make clear who supports what components of a deployed SDDC.
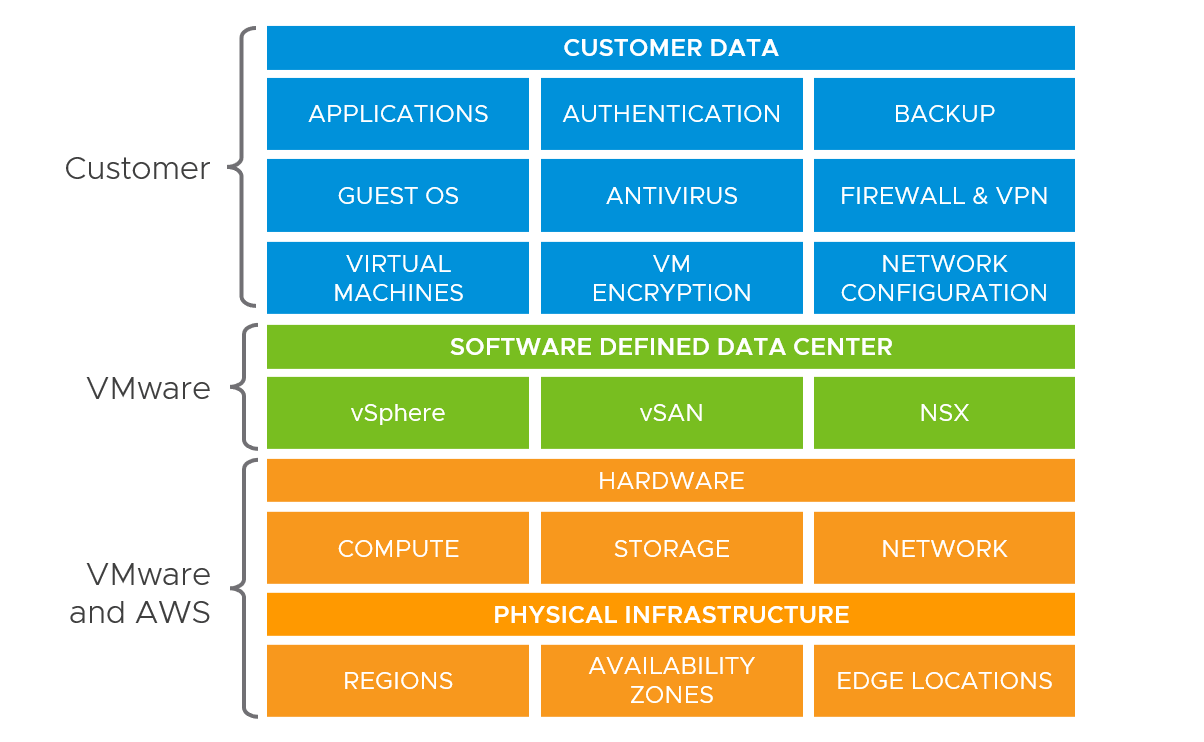 Working from the bottom up, the public cloud provider handles the design, implementation, and operation of the physical computing environment, including servers, networking, power, and other obligations within their data center facilities. This also includes regulatory compliance certification of those components, where required.
Working from the bottom up, the public cloud provider handles the design, implementation, and operation of the physical computing environment, including servers, networking, power, and other obligations within their data center facilities. This also includes regulatory compliance certification of those components, where required.
From there, VMware manages the configurations of the physical equipment that the cloud provider supplies, as well as the relationship to the cloud provider themselves. VMware installs, maintains, secures, patches, and upgrades ESXi, vCenter Server, NSX, vSAN, and other infrastructure management components that are required for an SDDC. VMware does this seamlessly by using classic vSphere resiliency features, like DRS, HA, vMotion, and the like. Where outages may be noticed, such as with an update to vCenter Server, notifications will happen via email to SDDC administrators.
Customers handle the workloads, data, choices about availability, and the methods of accessing workloads and data over the network. VPN configurations, public IP addresses, and network security are managed by customers as well.
