Feature Brief: vCenter Roles
Introduction
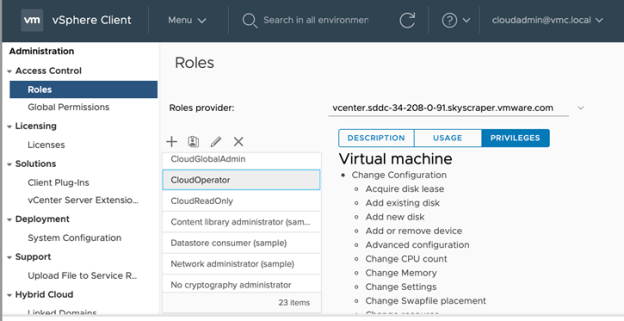
VMware Cloud on AWS offers the CloudAdmin role out of the box to allow customers to manage vCenter objects and for vCenter administration. A user with the CloudAdmin role can modify or view vCenter objects as well as delegate access to others in the organization to be cloud administrators. However, while this role offers the highest permissible level of access for our customers, often cloud administrators don’t always want to make every other user in their organization a CloudAdmin, but rather offer users a restricted subset of the privileges.
Flexible Permissions Model for Role-Based Access
Customers have the ability to create custom roles from a subset of the privileges from the current CloudAdmin role to offer more granular role-based access to vCenter objects.
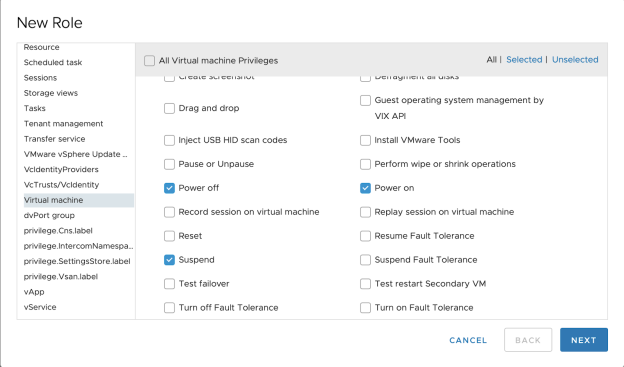
One such example of customization is to provide a subset of users with read-only access to VMs rather than full permissions to modify and delete VMs.
Access to the Complete Inventory Tree
Customers have the ability to apply permissions at any level of the inventory tree, while still protecting the management objects. This allows customers to run existing on-premises scripts on the cloud inventory without major modifications.
We continue to provide the compute and management resource pools for compute and management VMs respectively. However, due to added flexibility in the RBAC model, you could create VMs outside of the compute RP. While this flexibility exists, there cloud be potential resource contention issues between VMs that are created outside the Compute Resource Pool and within it as explained here. In order to limit contention across the VMs that you create, we strongly recommend that you continue to use the Compute Resource Pool as the location to create your VMs.
