Point-to-site VPN connectivity to Google Cloud VMware Engine is changing -- where to begin
With Google Cloud VMware Engine, a secure connection to the management network is required to manage the infrastructure components such as VMware vCenter, NSX, and HCX. This makes a point-to-site VPN very useful for accessing the environment after initial deployment, as well as for a backup just in case the on-premises interconnect circuits are disrupted. While earlier versions of Google Cloud VMware Engine private clouds included a point-to-site VPN gateway for this purpose, recently it was announced this feature is being discontinued. Fortunately, it is very simple to deploy your own VPN gateway from the Google Marketplace.
A new option for customers
Anyone who has created a new project within Google Cloud VMware Engine will quickly notice that the VPN Gateways section in the Network console is now grayed out (Figure 1).

Figure 1: Networking screen – VPN Gateway option grayed out
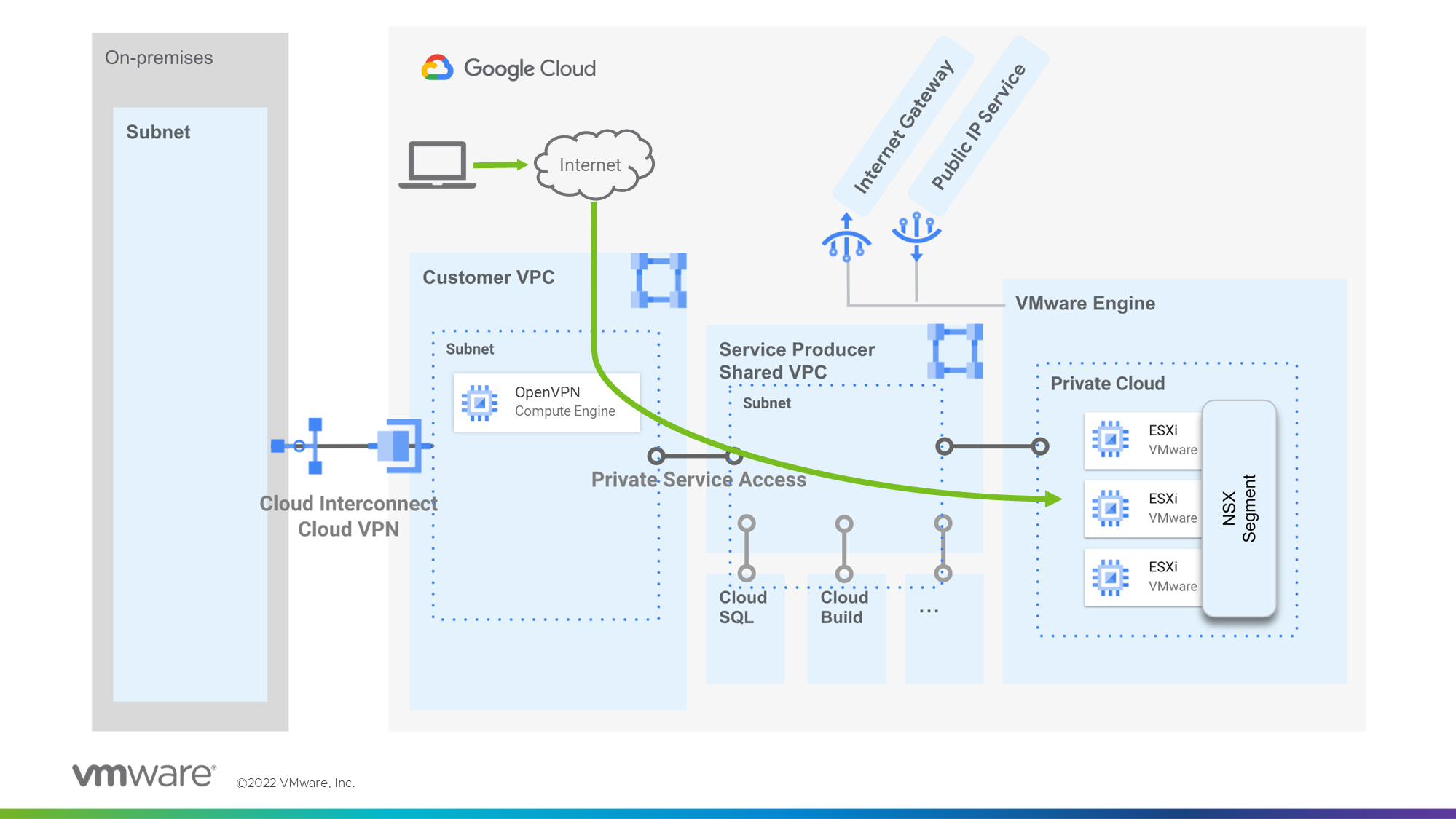
As an alternative, Google suggests deploying a marketplace vendor solution such as OpenVPN Access Server. This appliance is deployed as a Google Compute Engine instance, so setting up private services access between the VPC and the Google Cloud VMware Engine private cloud is a required prerequisite (Figure 2).
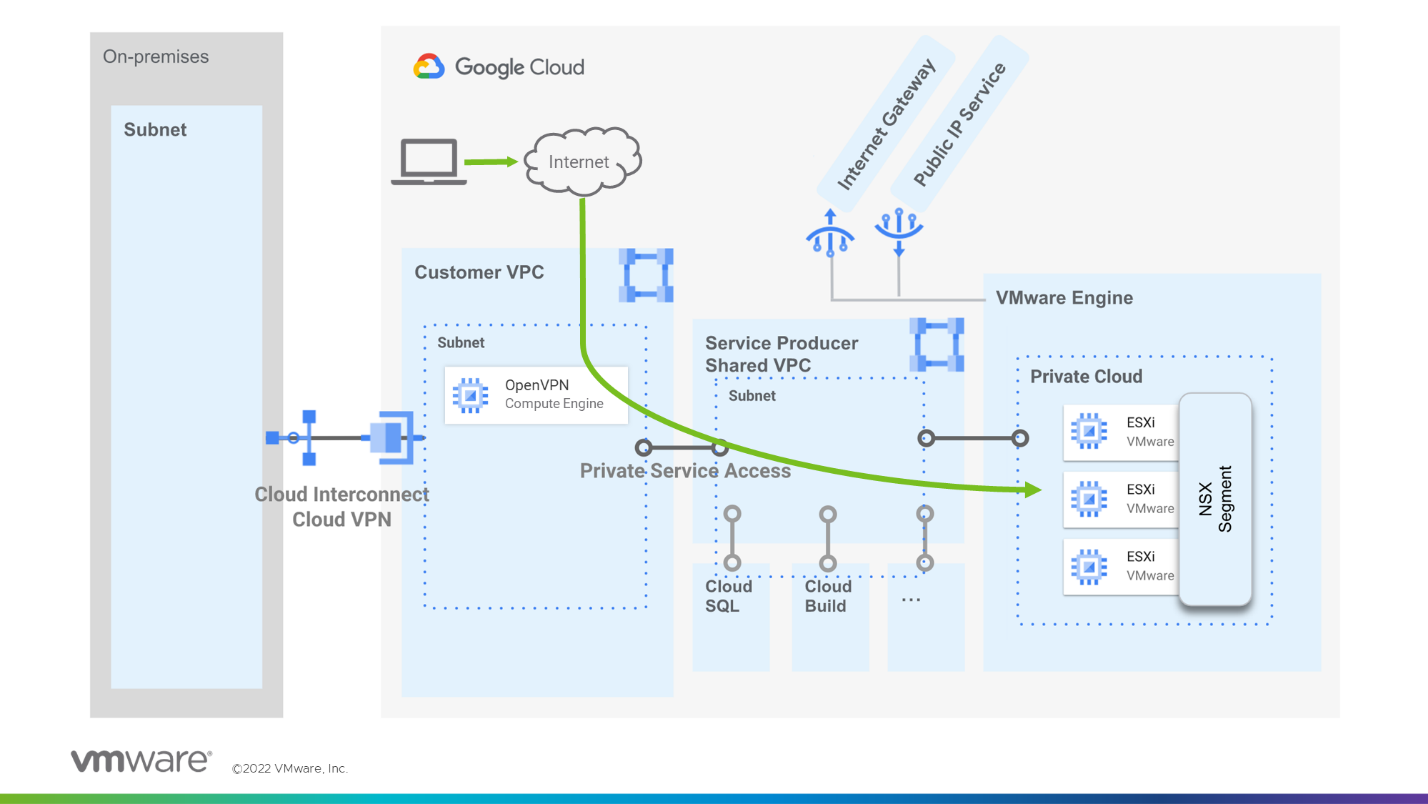
Figure 2: OpenVPN Access Server access into the Google Cloud VMware Engine Private Cloud through private services access
How to install the OpenVPN Access Server
To get started deploying the OpenVPN Access Server, check out these videos:
Google Cloud VMware Engine Point-to-Site VPN Configuration:
Prerequisite: If you have not already configured your private services access connecting your VPC to your VMware Engine private cloud, the following video will walk you through how to carry out those steps first:
Conclusion
Every IT pro understands that setting up a management VPN for backup access to the environment before you need it is a good idea. We hope you found the information in this blog helpful for setting up point-to-site VPN connectivity with Google Cloud VMware Engine. For more demo videos on configuring your environment, check out the Google Cloud VMware Engine Quick Start activity path.
